We had the privilege of speaking with Steven Sim, Chair of the OT-ISAC Executive Committee, during the recent summit in Singapore. As a seasoned expert in operational technology (OT) cybersecurity, Sim shared valuable insights into the importance of information sharing, the growing threat of ransomware, and the transformative role of AI in cybersecurity.
Kicking off the podcast, Steven introduced the Executive Committee and its pivotal role in driving OT-ISAC’s mission to foster a collaborative community and promote best practices. By providing advisory support and strategic guidance, the committee ensures OT-ISAC stays at the forefront of cybersecurity initiatives.
Balancing Information Sharing and Confidentiality
One of the most pressing challenges in OT cybersecurity is striking the right balance between information sharing and safeguarding sensitive data. He explained that OT-ISAC has implemented robust measures, such as the Traffic Light Protocol and data anonymization techniques, to protect confidentiality while promoting collaboration. The platform also employs protocols like STIX and TAXII to automate the exchange of cyber threat intelligence, enabling members to quickly share and respond to emerging threats.
Cross-Jurisdictional Collaboration
With cyber threats spanning borders, cross-jurisdictional collaboration is essential. Sim highlighted that OT-ISAC allows members to share threat intelligence across different regions without breaching data sovereignty regulations by anonymizing the information sources. This approach strengthens global defenses against transnational cyberattacks.
The Growing Threat of Ransomware
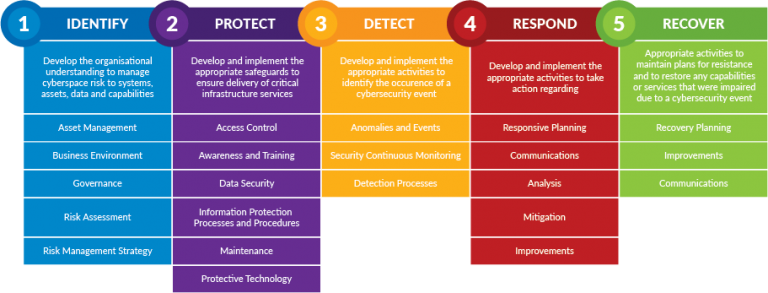
Ransomware remains a significant risk to OT environments. Steven urged organizations to avoid paying ransoms, citing the risks and long-term consequences. Instead, he emphasized the importance of investing in strong business continuity and incident response plans. By focusing on resilience and preparedness, organizations can minimize their exposure to future attacks.
AI’s Role in OT Cybersecurity
He also discussed the potential of AI in OT cybersecurity, noting its ability to streamline incident response and improve threat detection. However, he cautioned that while AI offers powerful advantages, it must be implemented with human oversight to manage the risks associated with automated systems.
Steven Sim has worked for more than 25 years in the cybersecurity field with large end-user enterprises and critical infrastructures, undertaken global CISO role, driven award-winning CSO50 security governance and management initiatives and headed incident response, security architecture, technology, awareness and operations at local, regional and global levels. He leads cybersecurity across large MNC, heading 8 direct reports at Group Cybersecurity Department as well as indirect reports across regional offices and local business units in 42 countries.
He oversees both IT and OT Security Governance, Global Cybersecurity Technology Management and Incident Response as well as Cyber Security Masterplan Office.
Always keen to give back to the community, he also volunteers at the ISACA Singapore Chapter (which won ISACA Global Outstanding Chapter Achievement in 2022) as the President (from 2021 to 2022) and OT-ISAC (since 2021), the second key thrust of the SG’s OT Cybersecurity Masterplan 2019, as Chair Executive Committee, as well as member of Geneva Dialogue Technical Community, and holds Masters in Computing, CCISO, CGEIT, CRISC, CISM, CISA, CDPSE, CISSP as well as technical certifications GICSP, GREM, GCIH and GPPA.
Recorded 5th Sept 2.30pm. Singapore Operational Technology Information Sharing and Analysis Summit 2024
#otcybersecurity #mysecuritytv #cybersecurity #singaporecybersecurity