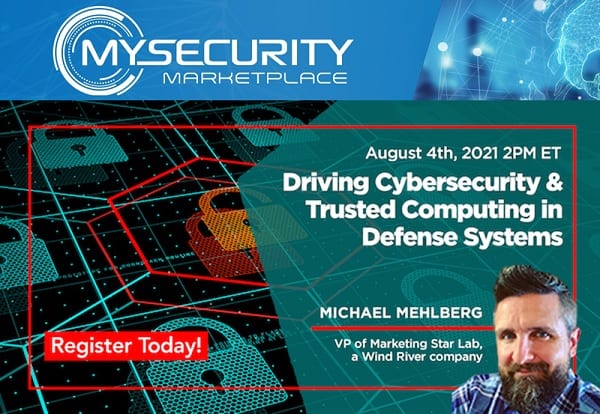
Driving Cybersecurity and Trusted Computing in Defense Systems
Embedded computing for military applications is vulnerable to cyberthreats like every other system. Threats are prevalent throughout every part of the system from the ICs to the signal-board computer to the software. Trust needs to be assured with each hardware component and software element. This webcast of military embedded computing experts will discuss how to […]
Driving Cybersecurity and Trusted Computing in Defense Systems Read More »