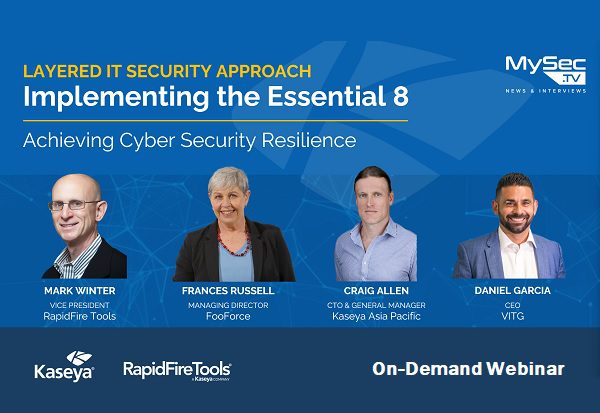
Layered IT Security Approach – Implementing the Essential 8
This session will discuss a layered approach to IT Security and how to implement the Essential 8 to achieve Cyber Security Resilience. About this event Register now for this webinar to discover: How a multi-layered security approach works The main areas of each layer of security The common types of solutions across security layers How […]
Layered IT Security Approach – Implementing the Essential 8 Read More »